IMPORTANT: The scanning tools introduced below may choke your web application with heavy traffic so proceed with caution and permission!
Kali Linux
So what's the easiest way for a layman to start? I discovered the path with least resistance is to download Kali Linux. Kali is a freely distributed Debian-based Linux system pre-loaded with many vulnerability scanners and hacking tools which are what I was after. Since I already use VirtualBox, the quickest way to get it up and running is to download the Kali Linux virtual box image from:
https://www.offensive-security.com/kali-linux-vmware-virtualbox-image-download/
The image is about 2 GB so be patient. If you prefer the Kali Linux ISO image instead, it's also available at:
https://www.kali.org/downloads/
Once you have downloaded the VirtualBox image, you can create a new virtual machine in VirtualBox by going to File > Import Appliance. It took a few minutes to create the virtual machine, for example, on a Mac Pro.
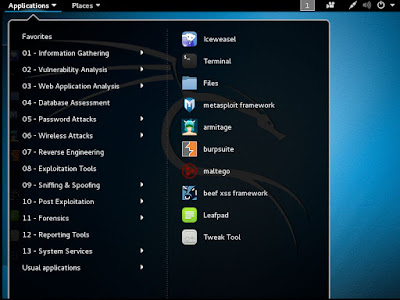
Now, launch the new virtual machine and log in as root. The default root password is "toor". There are many tools to choose from. Here's a screenshot of what's under the Application menu.
Nikto
One of the scanning tools under Application > Vulnerability Analysis is Nikto. From the official website:
"Nikto is an Open Source (GPL) web server scanner which performs comprehensive tests against web servers for multiple items, including over 6700 potentially dangerous files/programs, checks for outdated versions of over 1250 servers, and version specific problems on over 270 servers. It also checks for server configuration items such as the presence of multiple index files, HTTP server options, and will attempt to identify installed web servers and software. Scan items and plugins are frequently updated and can be automatically updated."
For usage information, please refer to the Nikto official website at https://cirt.net/nikto2-docs/
The command to start a Nikto scan is nikto -h www.my_website123.com. While scanning, Nikto reports potential vulnerabilities to the command console as they are found:
- Nikto v2.1.6
---------------------------------------------------------------------------
+ Target IP: X.X.X.X
+ Target Hostname: www.my_website123.com
+ Target Port: 80
+ Start Time: 2016-05-17 12:27:25 (GMT-4)
---------------------------------------------------------------------------
+ Server: Apache
+ Retrieved x-powered-by header: PHP/4.1.1
+ The anti-clickjacking X-Frame-Options header is not present.
+ The X-XSS-Protection header is not defined. This header can hint to the user agent to protect against some forms of XSS
+ The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type
Different scanners may discover new problems other scanners have not reported so you should try to run a few of them. It's also very likely that some of the reported problems are false positives or not exploitable by hackers so don't panic.
OpenVAS
There are also other scanners not bundled with Kali Linux One of them is OpenVAS. To install OpenVAS on Kali Linux, please refer to:
https://www.kali.org/penetration-testing/openvas-vulnerability-scanning
If your scan finish quickly (<1 minute) and returns without any problems found, chances are your server isn't responding to ICMP requests instead of being absence of vulnerabilities. You should set "Alive Test" to "Consider Alive" for your scan target.
On the other hand, if your scan finish quickly (<1 minute) and returns with an "Internal Error" and you are using OpenVAS Manager 6.0.5, it's a bug. Find out which version you have at the terminal by running
openvasmd --version
Then, check if the error log at /var/log/openvas/openvasmd.log shows:
md main:WARNING:2016-05-17 19h06.25 UTC:26326: sql_prepare_internal: sqlite3_prepare failed: no such table: current_credentials
To fix this, manually add the missing table to the sqlite3 tasks.db file:
CREATE TABLE IF NOT EXISTS current_credentials (id INTEGER PRIMARY KEY, uuid text UNIQUE NOT NULL);
Other Tools
In addition to OpenVAS, there are also other scanners readily available to download and install. Some of the ones I have found are:
Arachni - apt-get install arachni
Vega - apt-get install vega
At the time of writing, Vega is packaged with a graphical user interface but not Arachni. If you're trying Arachni, note that a scan may take a long time to finish (as in days or longer) because of its comprehensive nature but it's possible to optimize for faster scans.
Hopefully, this will get you started on securing your web application. Cheers!
No comments:
Post a Comment